We present the new Maikii product, the Privacy Set, the right way to protect your personal and private data.
In everyday life, in fact, these data are at risk on several occasions of which we are not aware. These moments are often linked to the use of those technological devices that we love so much and that improve the day. Fast payments, real-time information, movies and games on the move, video conferencing at work, and all the possibilities that technology offers and which you could no longer give up.
But every device we use is the bearer of secrets, private conversations and personal or business information that we do not want to make public, or at least we would like to decide to share.
But unfortunately digital devices are subject to intrusions and violations, a reality that we must take note of. In this article we will tell you about three cases in which to be careful and how to protect your privacy.
Charging your smartphone with a public USB port
Our smartphone is now a life partner, but if we don’t want to see it so romantically, it is at least a travel companion. The mobile phone travels with you all day, and it is essential that it is always charged especially for those who work on the go. But you know, the battery does not stand the strains of a full day.
And here, at the airport or in some public office, a charging point appears almost by magic: a USB socket, designed specifically to give lifeblood to your phone, of which you have the cable but not the adapter. In short, a real relief!
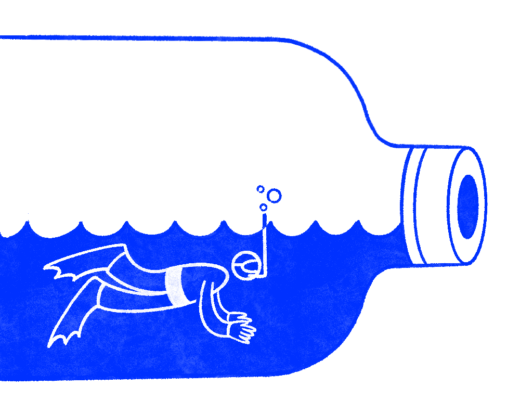
But the hidden danger lies precisely in that small universal plug. Those charging points provide easy access to your device for malicious hackers. In fact, the socket allows electricity to pass, but also allows data to pass. It would be like leaving an open car parked in the centre of a big city: on your return you could find it whole or just the bodywork.
No worries! There is a gadget that can solve the situation. The solution is a USB data blocker, a USB adapter that acts as a filter with the socket to which the phone or tablet is connected. It is ideal when charging your smartphone from an energy source considered unsafe. The device in fact allows the passage of electricity while at the same time blocking the passage of data, both incoming and outgoing, and therefore keeps away attackers and malware that can infect the phone.
Use the contactless ATM
Paying with an ATM was never more pleasant and faster, thanks to the innovative contactless technology! In fact, the new ATMs use RFID (Radio-Frequency Identification) technology , a device that allows identification of data simply thanks to its proximity to a reader: entering the POS range, the card sends the requested data.
This small revolution also presents a risk: being a system that works by proximity, it simplifies life for criminals who want to clone your ATM. Approaching you in crowded places where personal space is reduced, the attacker could place the cloner in your pocket and steal your data.
But also in this case, don’t worry, there is a rescue system! The anti-RFID card looks like a simple card to be inserted in one of the sections in the wallet, even if it hides a surprise! In fact inside there is a real shield from data theft and the guarantee of total isolation from magnetic sources.
Being spied on by the computer camera
The risks of violation of privacy also invade our homes. Have you ever thought that someone could spy on you from your computer’s webcam? Unfortunately, it is neither rare nor difficult.
How can that be? Camfecting takes place thanks to malware, often hidden inside an attachment or a voluntarily downloaded program. These viruses seek a flaw in the operating system or management software to take possession of your integrated video camera and give the spy the opportunity to look at you, filming you, understand if you are at home and any other similar intent.
How to defend yourself?
- Avoid downloading attachments from unknown recipients or clicking on unwanted emails.
- Update your operating system and antivirus, regardless of the brand of your computer.
- Check the access rights to the webcam and microphone from the privacy settings.
- Download free software that warns you if someone is trying to take control of the webcam.
However, the most intuitive and immediate system is to cover the camera lens. Here you have the webcam covers, adhesive plates that can be opened and closed when needed, to prevent any voyeurs from seeing when you are not using it.
Fantastic Privacy Gadgets and where to find them
Now you are ready to defend yourself from attacks on your privacy. All you need is our kit dedicated to cyber security: the Privacy Set that Maikii offers you consists of a USB data blocker to take on the go, an anti-RFID card to be inserted in the wallet and 5 webcam covers for the computers of the whole family or the office team. It is a corporate gift of great value, both material and symbolic: those who receive it will be extremely grateful and will be well disposed to show your logo on the product!